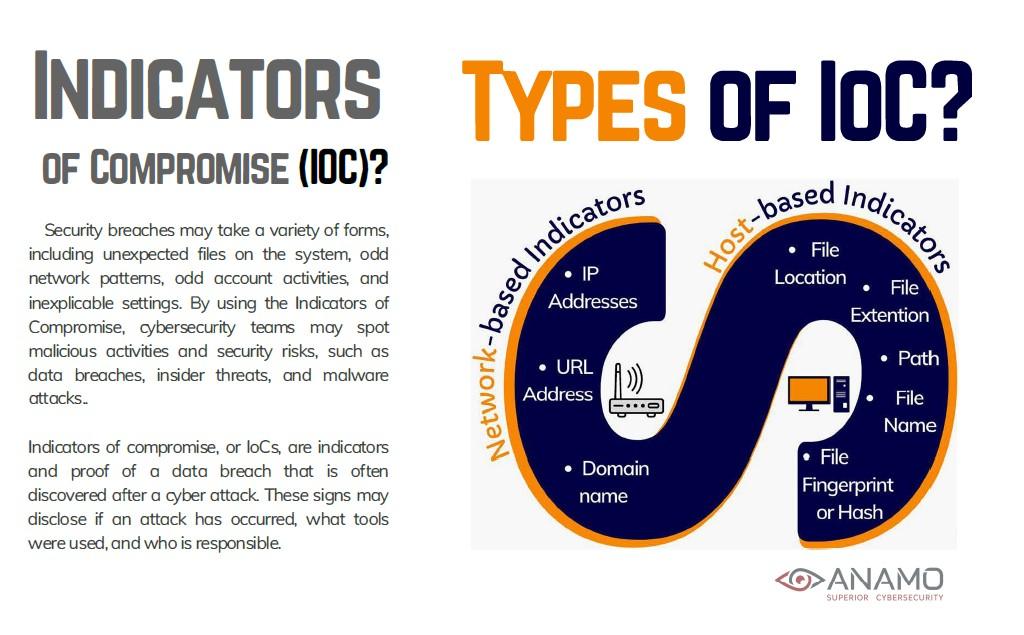
In cybersecurity, an Indicator of Compromise (IoC) is evidence suggesting a system or network may have been breached, helping security teams identify and respond to potential or ongoing attacks is exactly what US ProTech delivers with its Anamo CDM software that correlates Host-Based Indicators with comparative HashID Analytics.
Clearly, businesses face a multifaceted cybersecurity landscape packed deeply with Technical Adversaries who seek to breach networks, elevate credentials, and exfiltrate the maximum value and Data possible. Targets include Intellectual Property, Assets, Personal Identifiable Information and much more. Tools and threats include Data Breaches, Ransomware, Unauthorized Privileged Escalation, Phishing Attacks, Command Injection, Buffer Overflow, Social Engineering, Malware, and the list goes on!
Over the next four months, we’ll highlight 7 key cybersecurity topics, threats and data breach risks including:
- Cyberattacks: IoC Types & Impact
- User-Based and Insider-Threat Based Risks
- Industries at Risk
- Mitigation Strategies
- Artificial Intelligence Cyber Threats
- DNS Tunneling
- Insider Threats
This month let’s discuss the 1st of 7 important Cybersecurity considerations, “Cybersecurity IoC Types & Impact.” The overwhelming majority of Technology Executive and Cybersecurity leaders have absolute needs, these include:
-
Definitive evidence that something is happening, right now
-
To understand the significance and importance of the activity
-
Immediate identification where the activity is being presented
-
Having knowledge of options on how they need to respond
Essentially, software that correlates Host-Based Indicators of Compromise is the most effective process if delivering this information. By using the latest and most advanced comparative HashID Analytics, Cyber-practitioners are now capable of correlating data that has never been available until the advent of CDM. The concept of Continuous Diagnostics and Mitigation is over 10 years old with it’s origins dating back to 2013. Launched by CISA / DHS, today CDM is broadly used by over 300 Federal Agencies and is also commercially available as well. Anamo is a CDM that should be considered because it bridges the most significant attributes of SIEM, EDR, ASM, EPP, and other tools such as the gathering of data Forensics, delivery of eDiscovery, and more.
Here is an Explainer Video of Anamo CDM: https://youtu.be/ByTKwyAzZB4
Cyberattack: IoC Types & Impact
These attacks aim to make an online service unavailable to its users by overwhelming it with traffic.
These occur when unauthorized individuals gain access to sensitive data, leading to potential financial losses, reputational damage, and legal consequences.
A breach in a company’s supply chain or a third-party vendor can expose the entire organization to risk.
As businesses increasingly rely on cloud services, these become attractive targets for cybercriminals.
Data Breach Vectors:
- System intrusion: Cybercriminals gain unauthorized access to systems or networks.
- Web application attacks: Exploiting vulnerabilities in web applications to steal data or compromise systems.
- Miscellaneous errors: Human errors or misconfigurations can lead to data breaches.
- Stolen credentials: Using stolen usernames and passwords to gain access to systems.
- Human element: Employee mistakes or lack of security awareness can be a major source of data breaches.
- Insider threats: Malicious or negligent actions by employees can compromise data.
Contact US ProTech today to get your own free trial of Anamo CDM. You will immediately gain the insight needed to prioritize your security efforts. Allow Anamo CDM to deliver this essential data autonomously, automatically, and continuously, without any effort, complications, or any required scheduling on your part! Complimentary trials of Anamo CDM are available upon request, contact us online, by phone, or by speaking with a professional consultant or reseller, today.
Calendar for Future Topics:
April: User-Based and Insider-Threat Based Risks plus Industries at Risk
May: Mitigation Strategies plus Artificial Intelligence Cyber Threats
June: DNS Tunneling plus Insider Threats(IoC) is evidence suggesting a system or network may have been breached, helping security teams identify and respond to potential or ongoing attacks is exactly what US ProTech delivers with its Anamo CDM software that correlates Host-Based Indicators with comparative HashID Analytics.